Computer security is a discipline supposedly concerned with the integrity and confidentiality of information stored in a computer system. In any case, there is no technique capable of ensuring the inviolability of a system. At present, security is a major issue for societies as well as for the actors around it.
It should no longer be confined solely to the role of the computer scientist. Its long-term goal is to maintain the confidence of customers and clients. The medium-term goal is the coherence of the information system as much as possible. Network security serves to preserve the network against invaders, whether they are targeted attacks or opportunistic trojans.
Application security aims to preserve software and products against risk. A corrupted application could allow access to the data it is supposed to preserve to other parts of the house. A reliable security system can be recognized at the intent stage, which is before a program or device is deployed.
TOP 1 THE HACKER NEWS

 The Hacker News
The Hacker News
- New ChatGPT Lockdown Mode Limits Tools That Could Enable Data Exfiltration
- Free Apps Are Quietly Turning Smart TVs Into Web-Scraping Proxies for AI
- CISA Adds Actively Exploited SolarWinds Serv-U DoS Flaw to KEV Catalog
- AI Agent Uncovers 21 Zero-Days in FFmpeg; Chrome Patches Record 429 Bugs
- Miasma Worm Hits 73 Microsoft GitHub Repositories in Major Supply Chain Attack
TOP 2 : KILLPLOIT
TOP 3 : GB HACKERS

 GBHackers Security | #1 Globally Trusted Cyber Security News Platform
GBHackers Security | #1 Globally Trusted Cyber Security News Platform
- Cisco Catalyst Center Vulnerability Allows Attackers to Escalate Privileges
- Multiple Cisco Unified CCX Vulnerabilities Enable Arbitrary Command Execution by Attackers
- RONINGLOADER Uses Signed Drivers to Disable Microsoft Defender and Bypass EDR
- Hackers Exploit Rogue MCP Server to Inject Malicious Code into Cursor’s Built-In Browser
- NVIDIA NeMo Flaw Enables Code Injection and Privilege Escalation Attacks
- Cybercriminals Use Fake Invoices to Deploy XWorm and Steal Login Credentials
- Advanced macOS DigitStealer Uses Multi-Stage Attack Chain to Evade Detection
- Formbook Malware Campaign Uses Malicious ZIP Files and Layered Scripting Techniques
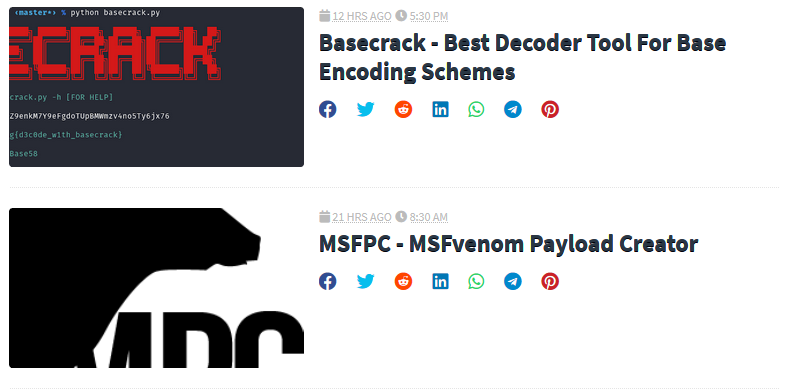
TOP 4 : ITECH HACKS

 iTech Hacks
iTech Hacks
- How to Change Home Address on Google Maps on Android, iPhone & PC
- Parental Controls Keep Resetting on iPhone or iPad? How to Stop It Permanently
- How to Change Your Home Address in Apple Maps on iPhone
- Fix: Asus Laptop Not Turning On or Won’t Boot (2026 Guide)
- Acer Laptop Won’t Turn On? 10 Easy Fixes to Bring It Back to Life (2026)
- How to Set Facebook Marketplace Settings to Local Only
- 10 Free Dating Sites With Unlimited Messaging Without Payment
TOP 5 : menlo security

 Menlo Security Blog
Menlo Security Blog
- What CISOs Need to Know About Modern Sandboxing Limitations - Blog | Menlo Security
- The Best VDI Alternatives for Hybrid Workforces in 2026 - Blog | Menlo Security
- Singapore's AI Leadership Demands a New Security Model: Why the Browser Can't Be Left Behind - Blog | Menlo Security
- Protecting Sensitive Data in Financial Services with AI Adaptive DLP - Blog | Menlo Security
- The Evolution of ClickFix: From Cleartext to Server Side Polymorphism - Blog | Menlo Security
